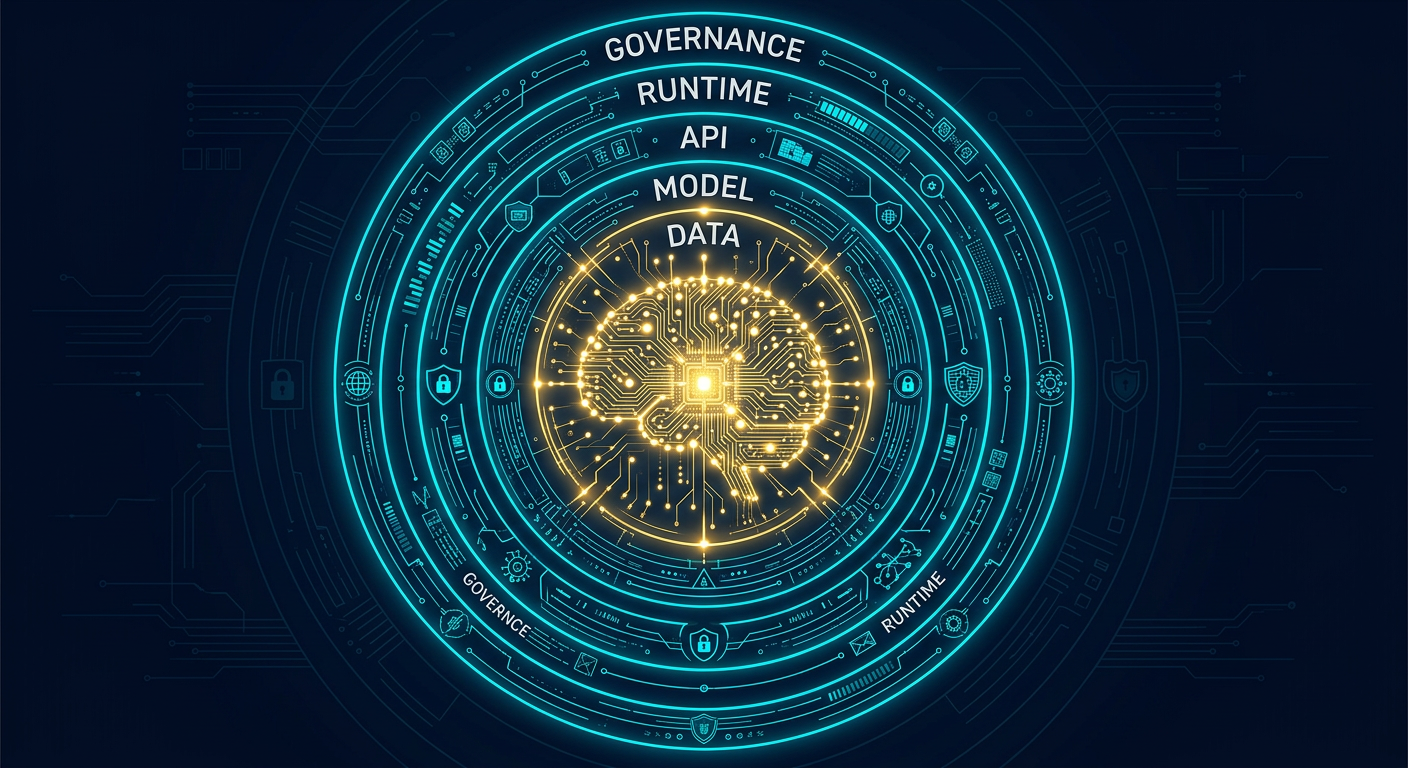
AI systems are now embedded in hiring pipelines, medical diagnostics, financial decisions, customer service, and national infrastructure. That expansion has outpaced the security frameworks designed to protect them. Traditional cybersecurity was built around defined perimeters, deterministic software behavior, and known attack vectors. AI systems break all three assumptions — they process natural language, generate unpredictable outputs, learn from data that can be poisoned, and expose interfaces that respond to inputs in ways that no static rule set can fully anticipate.
Securing an AI system is not an extension of securing a web application. It is a distinct discipline, and the organizations treating it as an afterthought are accumulating risk they cannot yet fully measure. This guide walks through every layer of that discipline — from the moment training data is collected to the day a model is retired — with concrete, actionable steps at each stage.
Why AI Security Is Different From Traditional Cybersecurity
Before getting into specific practices, it is worth understanding what makes AI security its own domain rather than a subset of existing frameworks.
A conventional application behaves exactly as its code instructs. An AI model, particularly a large language model, is a probabilistic system — its outputs are shaped by training data, fine-tuning, inference parameters, and the content of individual prompts. That probabilistic nature creates attack surfaces that have no equivalent in traditional software: you can manipulate an AI’s behavior without touching its code, simply by crafting inputs that push it in a direction its developers never intended.
The second difference is data centrality. In conventional security, data is what you protect. In AI security, data is also what builds the system — which means corrupting training data is a way to corrupt the system itself, invisibly and at scale, before a single user ever interacts with it.
The third difference is opacity. Neural networks, especially large ones, cannot explain their own reasoning. Security teams cannot audit an AI decision the way they can audit a log file. This makes detecting compromise and proving integrity fundamentally harder.
Frameworks like OWASP’s Top 10 for LLM Applications, the NIST AI Risk Management Framework, and MITRE ATLAS have begun mapping this territory systematically. The practices below draw on all three.
Layer 1: Securing Training Data
The security of an AI system begins with its training data. A model trained on corrupted, manipulated, or improperly sourced data will produce outputs that reflect that corruption — and the flaw will be invisible to anyone who only tests the finished model.
Audit every data source before ingestion. Know where your training data comes from, who controls it, and whether it has been modified since collection. Web-scraped datasets in particular carry significant risk: if an adversary knows a dataset will be used for training, they can seed it with content designed to create predictable model behavior at inference time — a technique known as data poisoning.
Establish and enforce data provenance records. Every dataset entering a training pipeline should carry a documented chain of custody: origin, collection date, preprocessing steps applied, and the identity of whoever approved it. Treat this with the same rigor as a software bill of materials.
Apply statistical anomaly detection to training datasets. Poisoned datasets often contain outliers — data points that are statistically unusual relative to the rest of the corpus. Automated profiling before training begins can surface these anomalies before they influence model weights.
Separate training, validation, and test data with strict access controls. Cross-contamination between these sets inflates benchmark performance and obscures real-world behavior. Apply role-based access controls so that the team validating a model cannot inadvertently (or deliberately) influence the data used to train it.
For fine-tuning on proprietary data: enforce data minimization. Only include data that is necessary for the target task. Sensitive records that are technically available but not relevant to the model’s purpose represent unnecessary exposure — both as a privacy risk and as a potential source of unintended model memorization.
Layer 2: Securing the Model Development Environment
The development pipeline — the infrastructure used to train, fine-tune, and evaluate models — is a high-value target that many organizations under-secure relative to their production environments.
Treat ML infrastructure with production-level security controls. Training clusters, experiment tracking systems, model registries, and artifact storage should all be subject to the same access control, logging, and monitoring standards as customer-facing infrastructure. A compromised training environment can introduce backdoors that survive deployment without any trace in production logs.
Version-control model weights and configurations. Every trained model should be stored with a unique identifier, a hash of its weights, the exact training configuration used to produce it, and the identity of whoever initiated training. This creates an auditable record that makes it possible to detect unauthorized modifications to model weights after the fact.
Sign model artifacts before deployment. Cryptographic signing of model files — similar to code signing in software distribution — allows downstream systems to verify that a model has not been tampered with between training and deployment. This is particularly important in supply chains where models are sourced externally or passed between teams.
Restrict who can trigger training runs. Unauthorized fine-tuning on a production model is an attack vector. Implement approval workflows for any process that modifies model weights, and log every training job with full parameter records.
Scan dependencies in your ML stack. Python ML environments accumulate deep dependency trees. Malicious packages — including typosquatted versions of popular libraries — have been documented in the PyPI ecosystem. Dependency scanning and pinned, verified package versions are non-negotiable for any model that will handle sensitive data or make consequential decisions.
Layer 3: Prompt Injection and Input Manipulation
For deployed LLM applications specifically, prompt injection is currently the most widely exploited class of vulnerability. It is the AI equivalent of SQL injection: an attacker embeds instructions inside a user input that override the model’s intended behavior, causing it to ignore system prompts, reveal sensitive information, take unauthorized actions, or generate harmful output.
Implement strict separation between system instructions and user input. Do not concatenate user-provided text directly into your system prompt. Use the model API’s native message structure — separate system, user, and assistant roles — so the model has structural context for which content is trusted instruction and which is untrusted user input.
Validate and sanitize all inputs before they reach the model. Define what valid input looks like for your use case — length limits, character restrictions, format requirements — and reject or strip anything that falls outside those bounds. This will not stop all injection attempts, but it eliminates the most trivial ones.
Apply output filtering before rendering model responses. A model that has been successfully injected may attempt to return instructions, code, or sensitive data in its response. Output filtering — pattern matching, classifier-based screening, or a second LLM pass dedicated to safety evaluation — adds a layer of defense after the primary model has generated its response.
Never grant an LLM direct, unreviewed access to high-consequence tools. If your AI application can send emails, execute code, modify databases, or call external APIs, every such action should pass through an approval layer before execution. Autonomous action based solely on model output is an injection attack waiting to be triggered.
Test explicitly for indirect prompt injection. Indirect injection occurs when malicious instructions are embedded in content the model retrieves from external sources — web pages, documents, emails, database records — rather than in the user’s direct input. Any RAG (retrieval-augmented generation) architecture is exposed to this vector. Test it specifically and treat retrieved content as untrusted by default. We break down the attack path and containment model in How Indirect Prompt Injection Exploits RAG Pipelines And 4 Controls That Actually Contain It.
Layer 4: API and Deployment Security
Most AI systems are accessed through APIs. Standard API security applies in full — and several AI-specific concerns layer on top.
Enforce authentication and authorization at the model API level. Every API call should require a valid, scoped credential. Use short-lived tokens rather than long-lived API keys wherever the architecture allows, and revoke credentials immediately on any indication of compromise.
Apply rate limiting and usage quotas per user and per application. Unusually high query volumes — particularly queries with systematically varied inputs — can indicate a model extraction attempt, where an adversary is trying to reconstruct model behavior or training data through repeated querying. Rate limits slow this class of attack and make it detectable.
Log all inference requests with sufficient detail to reconstruct attacks. At minimum, log the timestamp, user or session identifier, input length, output length, and any safety flags triggered. Full input logging is preferable where data regulations permit, as it is often the only way to investigate a successful attack after the fact.
Implement dedicated guardrail models at the API boundary. A lightweight classifier running in front of your primary model can screen inputs for known attack patterns — injection attempts, policy violations, off-topic queries — before they reach the model. This adds latency but significantly reduces the attack surface that reaches the primary model.
Separate inference endpoints by trust level. Internal tooling, partner integrations, and public-facing products should each use dedicated endpoints with separately scoped permissions and logging. Lateral movement from a compromised public endpoint to internal model infrastructure should be architecturally impossible, not just policy-prohibited.
Layer 5: Data Privacy and Model Memorization
Large language models are capable of memorizing and reproducing content from their training data. This is not a bug in the conventional sense — it is an emergent property of how these models learn — but it becomes a serious vulnerability when that training data contains personal information, proprietary content, or regulated records.
Audit training data for personal and sensitive information before training begins. Personal identifiers, financial records, health information, and internal communications should be identified and either excluded or de-identified before any dataset is used for training. The cost of this audit is orders of magnitude lower than the cost of a post-deployment data leak traced to model memorization.
Apply differential privacy techniques during training where regulations require it. Differential privacy adds calibrated noise to the training process in a way that limits the model’s ability to memorize specific records while preserving general statistical patterns. It carries a performance cost, but for models trained on highly sensitive datasets it is the strongest technical control available against memorization-based extraction.
Test your deployed models for memorization of sensitive content. Membership inference attacks and data extraction probes — where an evaluator systematically queries a model to determine whether specific records influenced its training — should be part of your pre-deployment security evaluation, not an afterthought. MITRE ATLAS documents the specific techniques adversaries use; test against those techniques in a controlled environment before your model is exposed to real adversaries.
Establish a clear policy for handling user input data in hosted AI products. Users of your AI application need to know whether their inputs are used to improve the model, retained for support purposes, or discarded after inference. This is both a regulatory requirement in many jurisdictions and a trust issue that affects how users interact with your system.
Layer 6: Monitoring and Incident Response
Securing an AI system at deployment time is necessary but not sufficient. The threat landscape evolves, models drift, and adversarial inputs that bypass guardrails on launch day may be actively circulating within weeks.
Implement continuous behavioral monitoring for your AI systems. Define what normal looks like for your model — typical output length, topic distribution, safety classifier hit rates, user satisfaction signals — and alert on meaningful deviations. A sudden increase in safety flag triggers, for instance, can indicate an active attack campaign against your system.
Build an AI-specific incident response playbook. Traditional incident response procedures assume that the compromised system behaves in known, bounded ways. AI systems do not. Your playbook needs to address scenarios specific to AI: a model that has been successfully jailbroken, a data poisoning attack that was not detected until after deployment, a prompt injection that caused the model to take unauthorized actions, and a model extraction attempt that may have exposed proprietary capabilities.
Define clear criteria for model rollback. Know in advance what observed behavior will trigger a rollback to a previous model version, and have that rollback executable quickly. A compromised or misbehaving model that remains in production because the rollback process is unclear or slow will cause significantly more damage than one that is pulled within hours.
Conduct regular red-team exercises against your AI systems. Hire or appoint adversarial evaluators whose explicit role is to break your model’s safety controls, extract its training data, hijack its actions, or cause it to violate its own policies. The findings from these exercises should feed directly into your security roadmap.
Layer 7: Governance, Compliance, and Organizational Accountability
Technical controls alone cannot secure an AI system. The organizational structures around that system — who is accountable for its behavior, how risk decisions are made, what regulatory requirements apply — determine whether technical investments are sustained and whether gaps are surfaced or buried.
Assign clear ownership for AI security. In many organizations, AI systems fall into a gap between the security team (which owns infrastructure) and the data science team (which owns models). Neither group has full visibility or authority. Designate a named owner — whether an AI Security Lead, a cross-functional committee, or a CISO with an explicit AI security mandate — who is accountable for the full security posture of each AI system.
Conduct a formal AI risk assessment before any model reaches production. This should cover: the sensitivity of data the model will access, the consequences of model failure or compromise, the attack vectors the deployment architecture exposes, and the regulatory obligations that apply. The output of this assessment should be a written risk acceptance record, signed by whoever has the authority to accept that risk.
Map your AI systems to applicable regulatory frameworks. The EU AI Act, NIST AI RMF, ISO/IEC 42001, and sector-specific regulations in healthcare, finance, and defense all impose security and governance requirements on AI systems. Regulatory non-compliance is itself a security risk — it creates legal exposure and signals to regulators and customers that your organization does not have its AI systems under control.
Establish a vendor security review process for third-party AI components. Most organizations building AI products are assembling systems from external models, datasets, APIs, and libraries. Each of those components is a potential supply chain risk. Require security documentation from AI vendors, review it before procurement, and revisit it on a defined schedule — model providers update their systems frequently, and a component that passed review twelve months ago may not pass review today.
Train every team that interacts with AI systems on security basics. Developers need to understand injection risks and secure API usage. Product managers need to understand what safe deployment looks like. Customer-facing staff need to understand how to recognize and report model misbehavior. Security is a shared responsibility, and it fails wherever it is treated as someone else’s problem.
A Consolidated AI Security Checklist
For teams that need a quick-reference summary, here is what the above practices reduce to in operational terms:
Before training: verify data provenance, scan for anomalies, remove sensitive records, apply data minimization.
During development: version-control all artifacts, sign model weights, restrict training pipeline access, scan ML dependencies.
Before deployment: conduct red-team evaluation, test for memorization, perform formal risk assessment, document rollback criteria.
At deployment: enforce API authentication and rate limiting, implement input validation and output filtering, deploy guardrail models, separate endpoints by trust level.
In production: monitor behavioral baselines continuously, log all inference activity, maintain an AI-specific incident response playbook, run scheduled red-team exercises.
Organizationally: assign named ownership, map to regulatory frameworks, establish vendor review processes, train all relevant teams.
The Bottom Line
AI security is not a product you can purchase or a checklist you complete once. It is an ongoing discipline that runs parallel to everything else your AI systems do. The organizations that build it into their development and deployment processes from the start will carry materially lower risk than those that layer it on after a breach forces the issue.
The attack techniques targeting AI systems are maturing rapidly. Prompt injection frameworks, model extraction toolkits, and data poisoning methodologies that were research curiosities two years ago are now in active adversarial use. The window for treating AI security as optional is closing — and for organizations that handle sensitive data, make high-stakes decisions, or operate in regulated industries, it may already be closed.
Start with the highest-risk layer in your current architecture — whether that is an unsecured LLM API, an unaudited training dataset, or the absence of any incident response plan — and work outward from there. The goal is not perfection on day one. The goal is a defensible posture that improves continuously, documented clearly enough that you can explain it to a regulator, an auditor, or a customer who asks the right question at the wrong moment.
Comments
No comments yet. Be the first to share your thoughts.
Sign in or create an account to leave a comment.